TACACS+ vs. Radius: What’s the Difference?
Organizations are looking at ways to protect their network as increased cyberattacks are infiltrating complex network systems. The rapid growth of artificial intelligence has also led to a steep rise in the number of complex attacks being attempted on organizational networks.
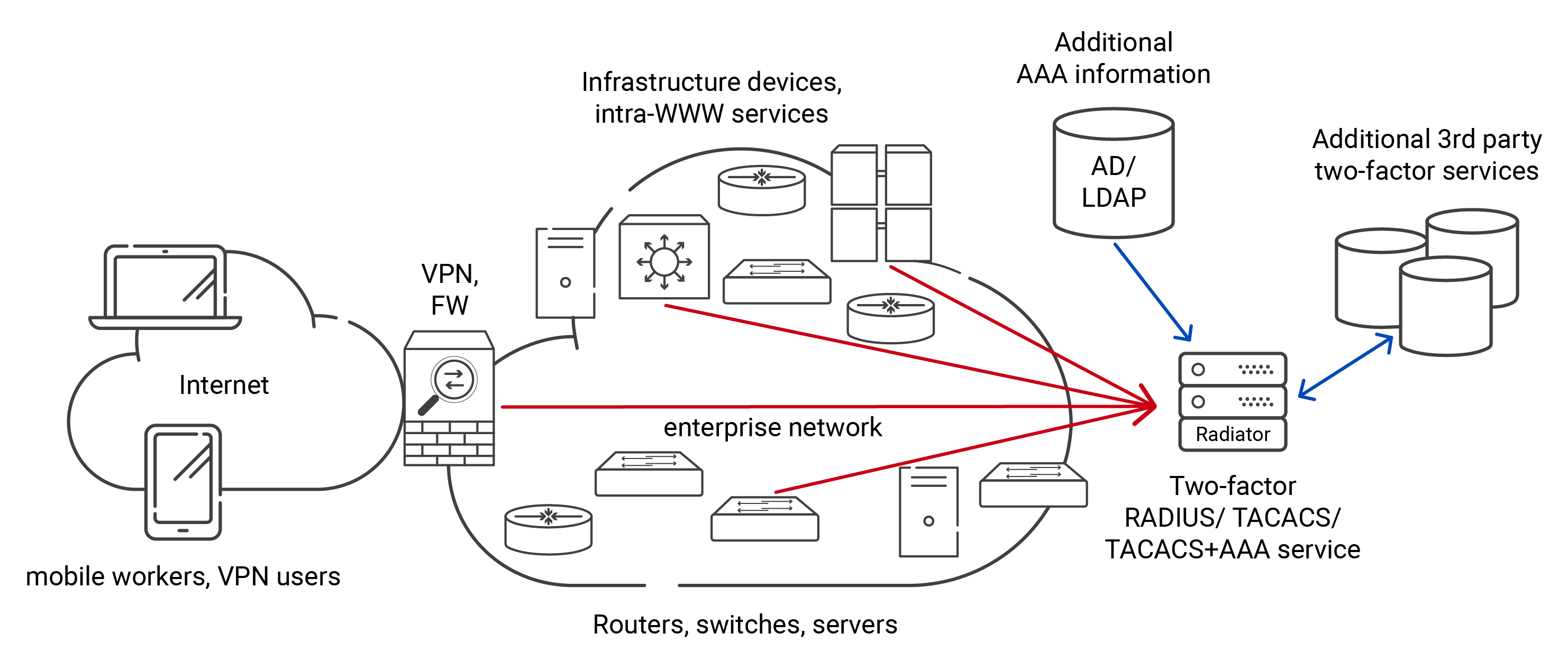
It is becoming increasingly difficult for administrators to view the users and devices that access the network, making the role of Authorization, Authentication, and Accounting (AAA) pivotal.
Historically, this meant protecting administrator logins to routers and switches. Today, it also includes users connecting to Wi-Fi, VPNs, cloud applications, and corporate resources.
Two authentication protocols frequently compared are TACACS+ and RADIUS. Both provide centralized authentication and accounting, but they were designed for different purposes. Understanding TACACS+ vs RADIUS is essential when choosing an access control architecture.
While older documentation often refers to TACACS, nearly all modern deployments use TACACS+, which improves security and functionality.
What Is TACACS+?
TACACS+ is a centralized authentication protocol used to control administrative access to network infrastructure devices such as routers, switches, and firewalls.
When an administrator logs into a device, the device sends the request to a TACACS+ server. The server validates credentials and returns permission decisions.
TACACS+ separates three security functions:
- Authentication
- Authorization
- Accounting
This separation allows detailed control over administrative actions. For example, an engineer may be permitted to view the configuration but not modify routing tables.
TACACS A High-Level Analysis
The Terminal Access Controller-Access Control System (TACACS) is a network protocol developed for centralized and automated authentication, authorization, and accounting of network devices like routers, switches, and firewalls. In 1984, CISCO developed TACACS and released it as an open standard protocol. From then on, the TACACS protocol mainly functioned as a network control protocol and helped administrators set user access controls for devices, resources, and network applications.
TACACS uses a central server that authenticates users and controls their access to network applications. It also monitors their activities on their managed CISCO devices and the CISCO server. When prompted, a user provides his username and password and is verified against their existing details in the database. The user can access the network and applications based on his authorizations if verified.
The TACACS+ has superseded the TACACS and provides a more secure option with enhanced encryption, support for authentication mechanisms like two-factor and multi-factor authentication, and transmission control protocol (TCP) for better communication.
How Does The TACACS Protocol Work?
The TACACS protocol functions on the client-server model, wherein a client (a remote server) requests to gain access to a network, and the TACACS server authenticates and authorizes the user to access the network.
- The remote access server first places an authentication request to the TACACS server.
- The TACACS server sends the access request packet to its database for verification.
- Upon verification of the user credentials, the TACACS server transmits the authorization to the remote access server.
- If the user can access the resource, the remote access servers grant or deny access based on the authorization message.
TACACS+ can manage attributes, define users and control authentication services. Administrators can set attributes through the options section in the operation framework of a service, file name, and shared secret key. The next part of the file consists of a group of users and groups to control accounting, authorization, and authentication. The TACACs+ follows the user = username or group = user name and is succeeded by the single and multiple attribute pairs placed inside curly brackets.
An authentication process starts when the client initiates a TCP session. The TCP transmits attribute pairs to the server in a standard header format followed by a variable length parameter field. An AAA request is captured as a header and sent in a clear format; the rest is sent as a parameter. This ensures the parameter field is encrypted for confidential, secure message transmission.
The TACACS variable perimeter provides extensibility and site-specific customization, and the TCP protocol provides a secure and safe delivery of the secret message. The server’s capacity, however, could be impacted by the format and protocol, as the format puts a load on the communication capacity of a server.
What Is RADIUS?
RADIUS stands for Remote Authentication Dial-In User Service. It authenticates users and devices attempting to access a network.
Unlike TACACS+, RADIUS is not limited to administrators. It verifies:
- Wi-Fi users
- VPN connections
- Remote employees
- Devices joining a network
When a device connects to a protected network, the access point or gateway forwards the request to a RADIUS server, which validates identity and returns a policy decision.
For more background on how centralized authentication works, see:
https://www.cloudradius.com/a-complete-guide-to-radius-servers/
TACACS+ vs RADIUS: Core Functional Differences
| Feature | TACACS+ | RADIUS |
|---|---|---|
| Primary Purpose | Device administration | Network access authentication |
| Typical Users | Network administrators | Employees and devices |
| Access Type | CLI and configuration access | Wi-Fi, VPN, and network login |
| Authentication Scope | Infrastructure control | User and device connectivity |
In simple terms, TACACS+ protects who can manage the network. RADIUS protects who can use the network.
Encryption Differences: TACACS+ vs Radius
Encryption is one of the most important technical distinctions between TACACS+ and RADIUS. Both protocols protect authentication traffic, but they do so in different ways and for different operational goals. TACACS+ prioritizes protecting administrative activity by encrypting the entire communication session.
At the same time, RADIUS focuses on securely validating identity while still allowing network devices to read certain authorization attributes needed to apply access policies.
| Security Feature | TACACS+ | RADIUS |
|---|---|---|
| Encryption | Entire packet encrypted | Password encrypted |
| Traffic visibility | Hidden | Partial visibility |
| Command protection | Yes | Not applicable |
| Session confidentiality | Strong | Moderate |
TACACS+ encrypts the full communication session, including commands. RADIUS encrypts authentication credentials but not all attributes. This design is intentional because RADIUS must interact with many networking devices and policies.
Understanding these differences helps determine which protocol better fits administrative security versus network access control.
Authorization and Access Control
Authorization is where the operational roles of TACACS+ and RADIUS become clear. While both protocols can approve or deny access, they control different types of activity after authentication succeeds. TACACS+ focuses on what an administrator is allowed to do once logged into a network device, whereas RADIUS determines how a user or device is allowed to access the network itself.
This difference in authorization granularity explains why organizations often evaluate TACACS+ vs RADIUS based on whether they need to protect infrastructure management or regulate network connectivity.
TACACS+ Authorization
- Controls administrator privileges
- Command-level permissions
- Configuration restrictions
RADIUS Authorization
- Assigns network policies
- VLAN assignment
- Device posture policies
- Conditional access
RADIUS is better suited for enforcing who can connect to the network and under what conditions.
TACAS+ Use Cases and Benefits
TACACS+ is typically used in enterprise networks to access network devices, emphasizing scalability, security, and adaptability.
Some routine use cases of the TACACS+ protocols include:
- Authorizing Users for Remote Access:TACACS+ is used to authenticate users, typically in an extensive network, to access network devices, applications, and resources through a VPN.
- Authorizing Devices for Network Access: TACACS+ authorizes only known network devices like access switches and firewalls to access the network.
- Validating Remote Access Server: TACACS validates various servers like the web and database servers to grant access to users on the network.
Accounting and Logging
Accounting and logging further highlight the different purposes of TACACS+ and RADIUS. Both protocols record authentication events, but the type of activity they monitor reflects what each protocol is designed to protect. TACACS+ focuses on administrative accountability by tracking what administrators do after logging into network devices.
RADIUS focuses on connectivity by recording user sessions, device access, and network usage. This distinction helps organizations decide whether they need detailed oversight of infrastructure management or visibility into who and what is accessing the network.
| Logging Type | TACACS+ | RADIUS |
|---|---|---|
| Tracks admin commands | Yes | No |
| Tracks login sessions | Yes | Yes |
| Tracks network usage | No | Yes |
| Tracks device connections | No | Yes |
TACACS+ logs administrator actions. RADIUS logs network access activity.
Benefits of TACACS+
TACACS+, the modernized version of TACACS, offers many benefits compared to the TACACS protocol. First, TACACS+ is a more secure and centralized protocol for managing users and granting them access to a network. Some notable benefits of TACACS are listed below:
- Enhanced Security
- Scalable for growing networks
- Allows for centralized administration
- Enforces granular access control
- Provides data for accurate accounting
- Enhances Security
TACACS+ enhances security by supporting various Wi-Fi protocols like PAP, CHAP, and MS-CHAP. It also encrypts all the traffic between the user (client) and the server to safeguard any user credentials and traffic from vector attacks and unauthorized access. - Scalable For Growing Networks.
TACACS+ has been designed to handle extensive networks with many users and devices. The TACACS+ protocol is also economical, reliable, and provides ease of implementation. However, a TACAS+ network can only support CISCO’s NAS VPN, making it native to only CISCO-centric environments. - Allows For Centralized Administration of Network Devices
TACACS+ servers allow for a centralized administration; a network administrator can look at all the users and devices from a single access point in a server. Centralized access makes it cost-effective and reduces administrative complexity associated with controlling access on individual network devices. - Enforces Granular Network Access Control
TACACS+ allows network administrators to administer granular access control for users and devices. An organization can assign role-based, policy-based, and attribute-based access controls to users and devices by enforcing granular access controls. This ensures that only authorized users can access applications, resources, and data. - Provides Data For Accurate Accounting
TACACS+ maintains records of user activities like their in and out times, applications, resources accessed, and any commands they have executed during their session. The data can be used for audit and compliance processes and troubleshooting issues during the session.
RADIUS- A High-Level Analysis
The Remote Authentication Dial-In User Service, or RADIUS, is used widely as a network security protocol based on the client-server model. With the RADIUS protocol, clients like users and devices can place requests to access services from any location. RADIUS is user-friendly, effective, and scalable for growing businesses, thus emerging as an industry standard to attain the IETF standardization.
The mode of communication between a Network Access Server (NAS) and RADIUS functions is based on the User Datagram Protocol (UDP). The RADIUS authentication protocols are of utmost importance in the 802.1X architecture, where point-to-point protocol and Extensible Authentication Protocol (EAP) are utilized. They perform the function of AAA.
- Authentication – matches user credentials to verify identity.
- Authorization – determines user permissions.
- Accounting – tracks user network resources.
How Does The RADIUS Protocol Work?
Network Attached Storage (NAS) is typically a RADIUS client; the RADIUS server is a process initiated on a UNIX or Windows machine. The NAS client transmits user information to a specified RADIUS server and responds to the returned message. A RADIUS server typically receives requests to connect users, authenticate them, and then return the configuration details to the client for the requested service for a user.
A RADIUS server can also mimic a proxy client to another RADIUS server or different kinds of authentication servers.
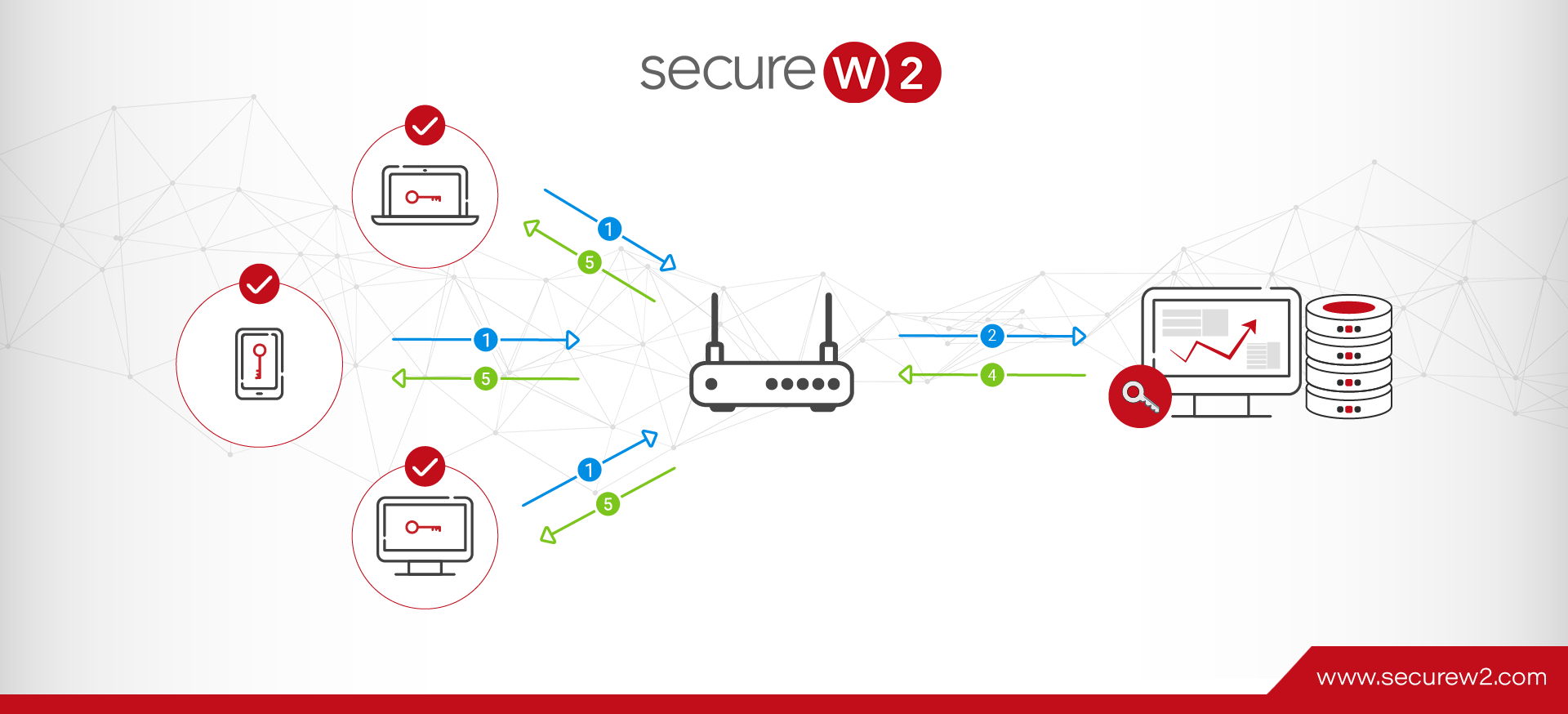
RADIUS Client Server and Dial-In user interaction:
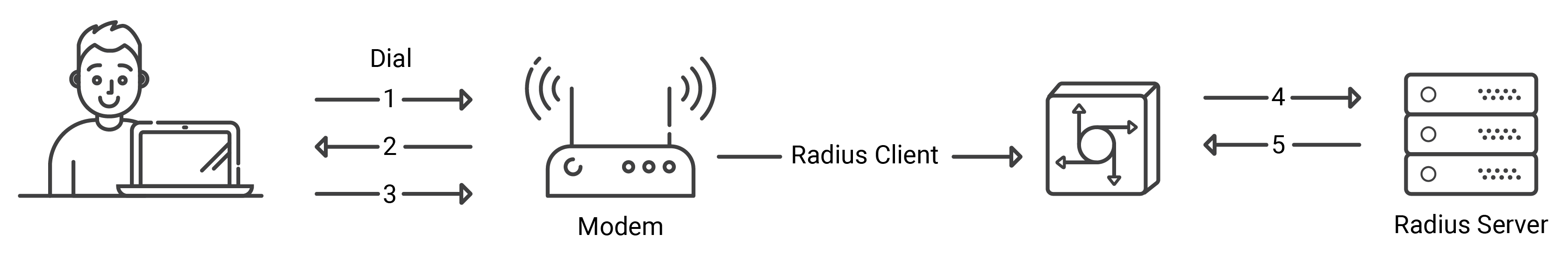
- A user places a PPP authentication request to the RADIUS Client, i.e., NAS.
- The NAS asks for credentials like the username and password in case of a Password Authentication Protocol (PAP) or challenge in case of a Challenge Handshake Authentication Protocol (CHAP).
- The user supplies the requested credentials.
- The RADIUS client sends the encrypted credentials to the RADIUS server.
- The RADIUS server presents a response in the form of Accept, Reject, or Challenge.
- The RADIUS client provides access to services and user resources based on Accept or Reject parameters.
Benefits of RADIUS
RADIUS provides a centralized AAA control for users who wish to connect to a network and has been accommodative of various protocols and modern networks. Though legacy AAA protocols still rely on on-premise servers, cloud-based RADIUS authentication is gaining popularity in modern network setups.
Some benefits of RADIUS include:
- Provides enhanced security benefits
- Enables 802.1X using EAP-TLS Protocol for CBA
- Integrates with numerous IT infrastructures
- Makes Granular Control and Management Easier
- Provides Enhanced Security Benefits
RADIUS supports various Wi-Fi and authentication protocols that provide unique credentials to users instead of shared keys alone. RADIUS also supports MFA and digital certificate-based authentication for enhanced user and device authentication security. - Enables 802.1X With EAP-TLS for Certificate-based Authentication
RADIUS enables 802.1X with the Extensible Authentication Protocol (EAP) framework for authentication. The EAP protocol helps transmit authentication packets between two components with ease. The EAP framework consists of many frameworks, like the PEAP-MSCHAPV2, which supports password-based authentication, and the more secure EAP-TLS authentication, which supports digital 802.1X certificates. - It integrates with numerous IT infrastructures.
Unlike on-premise setups, the modern Cloud RADIUS integrates with any IT system without needing a significant overhaul. You can add it to your existing infrastructure in layers for enhanced security. For example, you can divide your network into segments and enable level-wise authentication through digital certificates for crucial network resources, thus enhancing security. - Makes Granular Access Control Easier
RADIUS makes it easier to see who and what has access to what resources through VLAN monitoring and segmented attributes. This RADIUS-specific feature makes it a standalone protocol, ensuring only authorized users and devices can access sensitive information and applications.
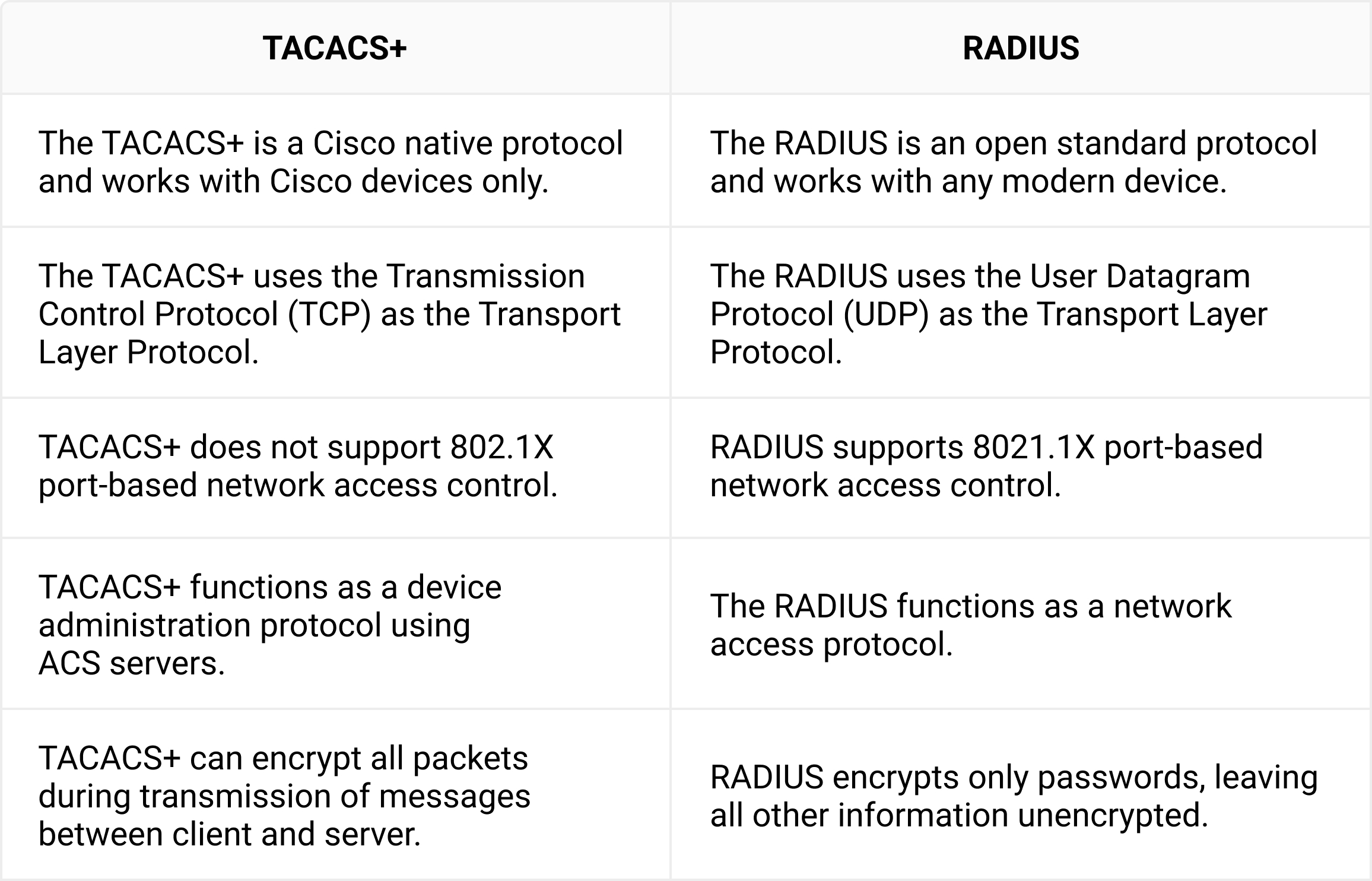
Difference Between TACACS+ and RADIUS
The most pertinent distinction between RADIUS and TACACS+ is that RADIUS is used to authenticate users to a network, while TACACS+ is used to monitor network devices like routers and switches. Here are some more differences between the TACAS+ and the RADIUS protocol:
TACACS+ vs Radius in Modern Networks
Today’s networks include mobile devices, cloud applications, and remote users. Access control must be based on identity, not physical location.
TACACS+ was built for static environments where administrators worked on-site. RADIUS supports dynamic environments with distributed connectivity.
| Capability | TACACS+ | RADIUS |
|---|---|---|
| Cloud support | Limited | Strong |
| Remote users | Not designed for | Fully supported |
| Device authentication | No | Yes |
| Zero Trust alignment | Partial | Strong |
Because modern organizations must continuously authenticate employees and devices, RADIUS often becomes the core authentication platform.
Can TACACS+ and RADIUS Be Used Together?
Yes. Many enterprises deploy both TACACS+ and RADIUS because they address different security layers. TACACS+ protects administrative access to infrastructure devices, ensuring only authorized personnel can manage routers, switches, and firewalls.
RADIUS, in contrast,, controls user and device connectivity to the network by authenticating access to Wi-Fi, VPNs, and other services. Used together, they provide complementary protection: TACACS+ secures who can operate the network, while RADIUS secures who can use it.
In summary:
- TACACS+ protects network administration
- RADIUS protects network access
RADIUS and TACACS+ solve different security problems. One controls administrators, and the other controls connectivity.
TACACS+ or RADIUS- The Better Choice For Your Organization
TACACS+ is a choice for industries with higher security demands like finance, security, and defense, where breaches are considered catastrophes. RADIUS provides easier integration and can be scaled to growing needs, unlike on-premise setups. It is the go-to choice for managing user access for educational institutions, internet service providers (ISPs), and small and mid-size enterprises with many users, managed devices, and BYODs.
TACACS+ and RADIUS are both excellent network security protocols per industry standards. However, every organization has specific needs and may want to weigh their choices before you can opt for a protocol to secure your network. RADIUS is the way forward if you are an organization looking for a simple, out-of-the-box implementation.
Suppose you are an organization with many devices, a mix of routers and switches that need to be secured, and also have to control user access for accounting purposes. Then RADIUS is the clear winner and a better choice.
Moving Toward Identity-Based Access
Traditional network security assumed that anything inside the corporate network perimeter could be trusted. Once a device is successfully connected, it often receives broad access to internal resources. This model worked when users were on-site, and devices were company-managed, but it breaks down in environments with remote workers, cloud services, and unmanaged endpoints.
Modern security strategies instead focus on identity verification at every connection attempt. Access decisions are no longer based solely on location, but also on the user, the device they are using, and whether that device meets security requirements. RADIUS supports this approach through policy-based authentication, device validation, and ongoing session control.
These capabilities allow organizations to continuously evaluate access and enforce restrictions dynamically, making RADIUS well-suited for Zero Trust architectures where trust is never assumed and must always be verified.
Centralized Authentication with CloudRADIUS
Cloud-based authentication services expand RADIUS beyond traditional networks. Instead of only authenticating Wi-Fi connections, centralized policy can control access across wired, wireless, and remote environments.
CloudRADIUS provides:
- Centralized authentication policies
- Detailed access logging
- Device and user verification
- Scalable network access control
Learn more here: https://www.cloudradius.com/features.
Choosing the Right Protocol for Modern Access Control
The TACACS+ vs RADIUS discussion is less about choosing a winner and more about understanding their roles. Each protocol was designed to protect a different layer of the environment. TACACS+ secures administrative control of routers, switches, and firewalls, ensuring only authorized personnel can manage critical infrastructure. RADIUS secures connectivity itself by verifying users and devices before they are allowed onto the network.
As organizations shift to remote work, cloud applications, and unmanaged endpoints, the security boundary is no longer the device configuration interface but the connection point. Most access now happens through Wi-Fi, VPNs, and remote services rather than direct console administration.
Because of this change, controlling network access has become the larger security priority. In many modern deployments, TACACS+ continues to protect infrastructure administration, while RADIUS serves as the primary foundation for identity-based access control across the entire environment.
Unify Authentication with CloudRADIUS and SecureW2
Today’s networks extend far beyond a single office. Users connect from home, devices move between networks, and applications operate across both on-prem and cloud environments. Protecting only administrator logins is no longer sufficient. Organizations need consistent authentication and enforceable policies for every user, device, and connection attempt.
CloudRADIUS provides centralized authentication, access policy enforcement, and detailed activity logging across wired networks, Wi-Fi, and remote access. SecureW2 complements this with certificate-based identity verification and automated onboarding, allowing devices to authenticate securely without relying on shared credentials or manual configuration. Together, they create a single, reliable source of truth for access decisions while improving visibility for security and compliance teams.
See how identity-based authentication can simplify operations and strengthen security across your entire environment.
Schedule a Demo: https://www.securew2.com/schedule-demo.
Leverage SecureW2’s CloudRADIUS For Seamless Integration
As an organization with growing business needs, network security is getting cumbersome, and organizations are looking for robust, foolproof security solutions. As an organization standing at the crux of growth, weighing your security options before choosing is very important. The TACACS+, a Cisco proprietary protocol, supports Cisco network devices, making it a better choice for larger organizations with rigid in-premise setups.
You can safely switch to SecureW2s CloudRADIUS, a wholly cloud-based RADIUS solution that integrates with your existing infrastructure without needing an overhaul. Our PKI solution helps you distribute digital certificates at the click of a button through Managed API solutions so that your users and devices are securely onboarded without the risk of misconfigurations.
Click here for more on our cloud-based security solutions for your organization.