Integrating Microsoft Entra ID with RADIUS Authentication
Are you moving all your applications to the cloud to authenticate against Microsoft Entra ID (formerly Azure AD), but don’t know how to implement RADIUS authentication for Wi-Fi or VPN with Azure?? Don’t worry, you’re not alone. Hundreds of organizations contact us every month with this problem.
Some organizations begin by performing an LDAP sync, duplicating their Azure AD on-premise as a way to tie network authentication to their cloud Azure AD. For organizations with existing credential-based 802.1X, this can be a good temporary solution that allows them to move to Cloud Azure AD or Microsoft Entra ID, but they still have to use their legacy servers. Configuration guides are hard to find, and often what you can find is difficult to configure. That’s why you need a better solution.
What is Azure RADIUS Authentication?
Azure RADIUS authentication is a method that allows network infrastructure to verify users and devices by communicating with Azure AD or Microsoft Entra ID through the RADIUS protocol. Since Azure AD does not include a native RADIUS server, organizations typically deploy an intermediary authentication service to bridge identity services and network access systems. This allows users and devices to authenticate for Wi-Fi, VPN, and other network resources while maintaining centralized identity control.
Most modern implementations rely on certificate-based authentication like EAP-TLS. Instead of validating passwords, the system checks digital certificates issued during enrollment using a passwordless authentication approach to reduce the risk of credential exposure.
Components of Microsoft Entra ID (Azure AD) RADIUS Authentication
A successful Azure RADIUS authentication deployment depends on coordination between identity services, certificate infrastructure, and network hardware.
Identity Platform — Azure AD / Microsoft Entra ID
Azure AD or Microsoft Entra ID acts as the central identity authority, where user attributes, group membership, and device compliance data can all be referenced during authentication decisions. Organizations can use this information to create granular network access policies that are based on roles or departments.
RADIUS Processing Layer
The RADIUS service sits between network gateways and identity systems. It evaluates authentication requests and determines whether network access should be granted. This layer is important because it enforces security policies before allowing traffic into protected resources.
Certificate Infrastructure
PKI forms the foundation of passwordless Azure RADIUS authentication. When a device is enrolled, a digital certificate is generated and stored securely on the endpoint. During authentication, the certificate is automatically presented without requiring manual password entry.
Device Management Integration
Mobile device management platforms such as Microsoft Intune can automate certificate distribution, renewal, and Wi-Fi configuration deployment. Automation reduces administrative workload and helps ensure consistent security enforcement across large device fleets.
How Certificates Enable RADIUS Authentication with Microsoft Entra ID or Azure AD
We’ve shown Azure customers how they can leverage digital certificates to tie Microsoft Entra ID to network security. Users/devices will perform a one-time enrollment process with their Azure AD (or Microsoft Entra ID) credentials to get an ultra-secure X.509 Digital Certificate. This certificate can then be presented to the RADIUS Server as a more secure way to validate active users in your organization.
Apart from being an easy way to tie RADIUS Authentication to Microsoft Entra ID, certificates have many benefits that passwords lack. They improve user experience, over-the-air security, decision-making context, and are future-proof. Microsoft has recommended that organizations move toward a passwordless authentication method, such as certificates.
Setting up a Public Key Infrastructure (PKI) allows you to easily issue and manage certificates for all your users and devices. You can integrate a Managed PKI to directly communicate with your Microsoft Entra ID or Azure AD provider to enroll the appropriate certificate to each user based on their standing in your organization.
Once you enroll the device with a certificate, you can configure Cloud RADIUS to authenticate users by using their issued certificates. Certificates allow administrators to segment users into separate groups. You can place your employees into different groups (HR, Marketing, IT, Accounts Receivable) and configure RADIUS to apply specific network policies to each respective user. It’s a good idea to do this at the time of authentication so users will be connected to Wi-Fi and given the correct amount of network access in seconds. Cloud RADIUS goes beyond perimeter security.
Leverage Endpoint Manager (or other MDMs) for RADIUS
For organizations with EM/Intune/GPO or other MDMs, you can push certificates, policies, and 802.1X configuration settings to easily control access for every managed device. Intune devices are guided through the certificate enrollment (+renewal) process. You can configure your Cloud RADIUS server to authenticate the user using their issued certificates. Cloud RADIUS can directly communicate with Microsoft Entra ID or Azure AD in order to authenticate the user’s identity for Wi-Fi/VPN access.
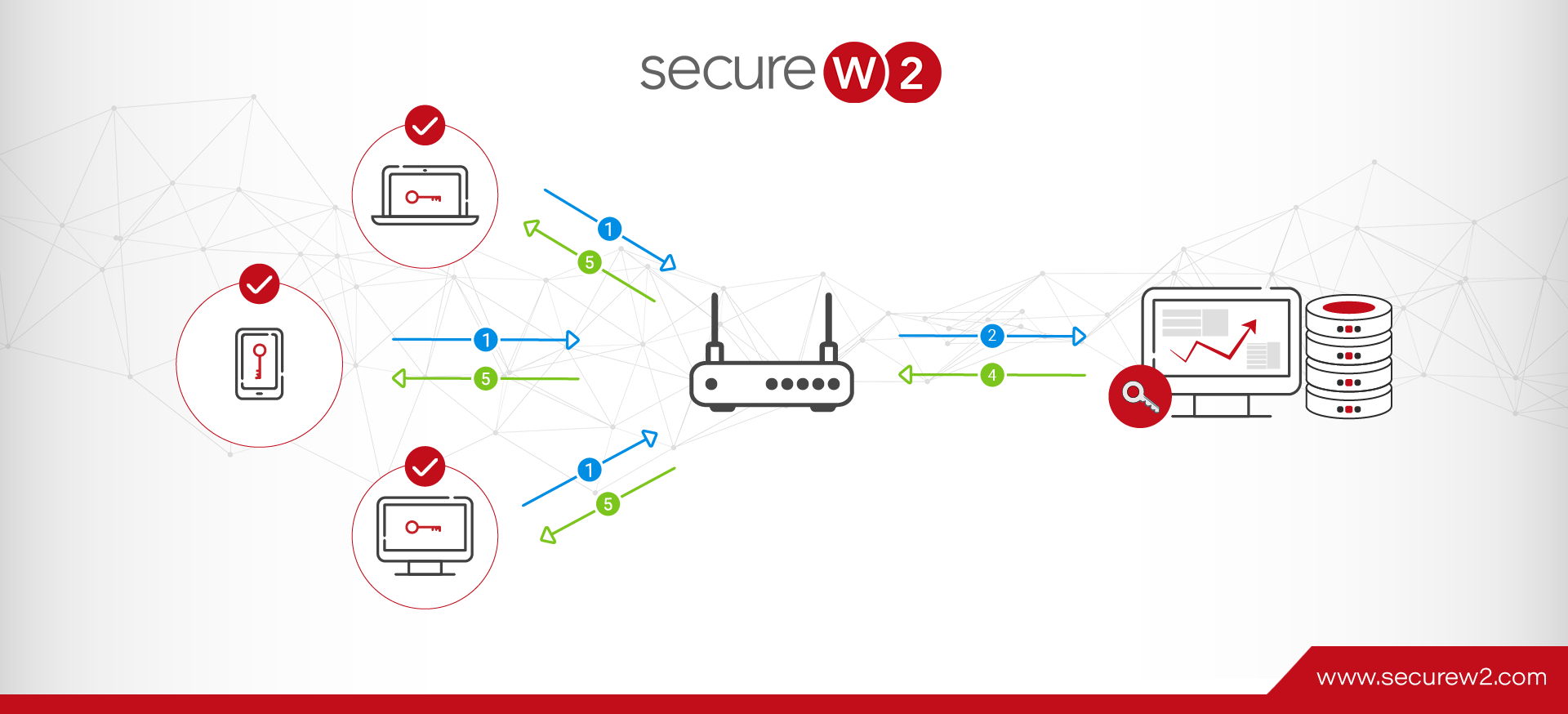
Below is a high-level overview of certificate enrollment/renewal and the ongoing authentication process.
For a more detailed guide, check out how to use SCEP to enroll certificates on Intune devices.
What If I Need to Connect Unmanaged Devices?
Enterprises that need to onboard unmanaged devices can integrate modern onboarding solutions that direct users to download a dissolvable client onto their device and enter their credentials. The client then verifies the user against their Microsoft Entra ID or Azure AD and assigns a custom certificate filled out with a user’s identifying information. The RADIUS server will then use the certificate to authenticate the user.
The SecureW2 self-service software,JoinNow MultiOS, allows users to configure their devices for 802.1X security. After downloading the JoinNow MultiOS Dissolvable Agent, users are redirected to an authentication portal where they enter their Azure AD credentials. The system verifies their credentials against your Microsoft Entra ID, and applies user/device information to the issued certificate with the appropriate policies. The system then installs the certificate in the device’s key store, generates a private key, and locks that key to the device.
Setting Up RADIUS Lookup in Azure AD (Now Microsoft Entra ID)
We’ve heard from many Azure customers that it’s difficult to set up RADIUS authentication because Azure AD, now Microsoft Entra ID, is limited compared to AD when it comes to supporting WPA2-Enterprise and 802.1X. Customers also need to move away from passwords as a form of authentication and replace them with digital certificates.
Here’s a quick overview of what you need to do for setup:
- Create an Azure AD Identity Lookup Provider
- Configure RADIUS Lookup in Azure Portal
- Configure Azure AD Attribute Mapping in SecureW2
- Configure Azure AD Policies in SecureW2
For the full documentation, head over to Configuring Dynamic RADIUS with Azure AD to Support WPA2-Enterprise.
Create an Azure Identity Lookup Provider
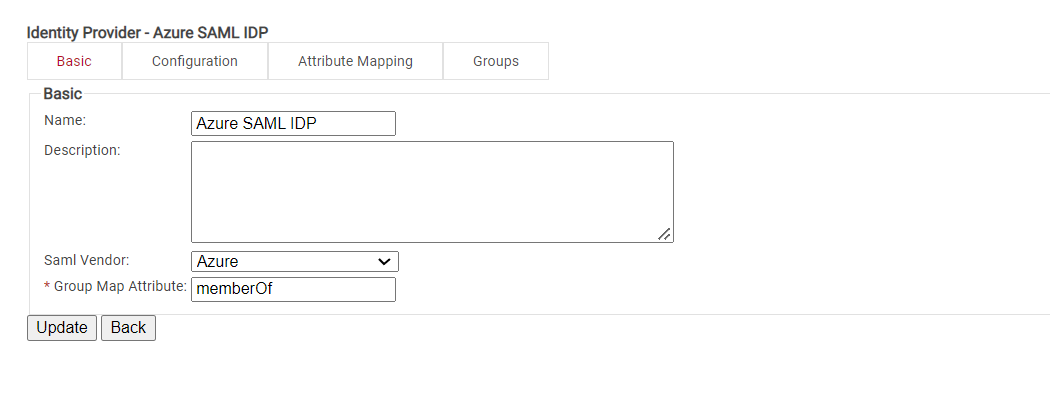
Creating an Identity Provider (IDP) in SecureW2 tells Cloud RADIUS how to connect to your Microsoft Entra ID or Azure AD user database, verify user credentials, and issue certificates.
Configuring RADIUS Lookup in Azure Portal
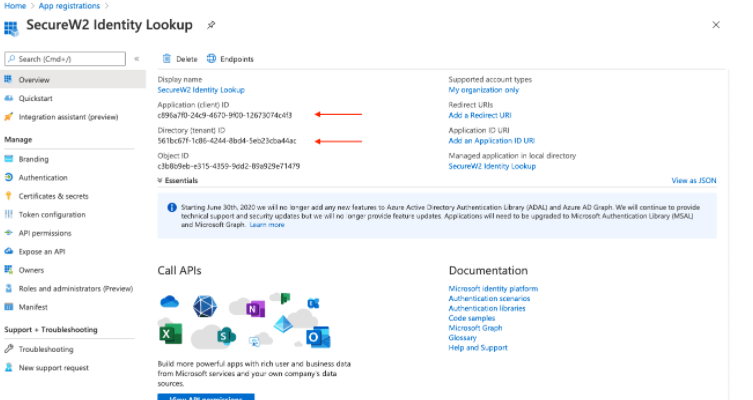
SAML applications provide a secure and efficient method for confirming the identity of valid users within the Identity Provider (IDP). By utilizing the SAML protocol, network admins can guarantee that only those users who are identified within the IDP are able to access the secure network. Their devices can also be enrolled for certificates, enabling highly secure passwordless authentication.
Configuring RADIUS Identity Lookup with Azure AD Attributes & Policies
Network authentication with Azure AD or Microsoft Entra ID is powerful because admins can use identifying attributes from the service in their network policies. By mapping Azure AD attributes with SecureW2, admins can segment users/devices/groups into their own VLANs, ensuring no user can access resources which they aren’t allowed.
You can configure Cloud RADIUS to check user status every time the user requests authentication to the network so they can be segmented properly. Below, we provide a quick guide on how to use Azure AD attributes to create network policies.
Configure Azure AD or Microsoft Entra ID Attribute Mapping
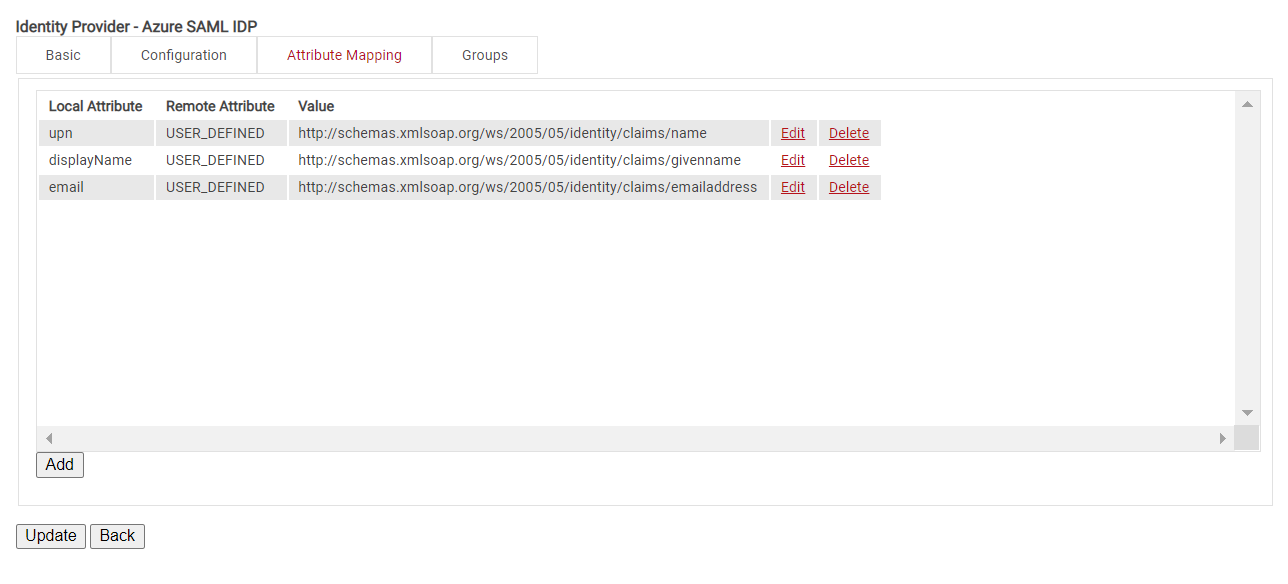
This is where you can map out the attributes sent by Azure AD or Microsoft Entra ID and encode them onto certificates. Customizable attributes and schemas allow you to create “templates” for new objects that streamline the provisioning process. For example, a user assigned the “Marketing” department value can automatically be assigned new properties according to the synchronization rules when they are reassigned to the “Sales” department to reflect their new permissions.
Configuring Groups
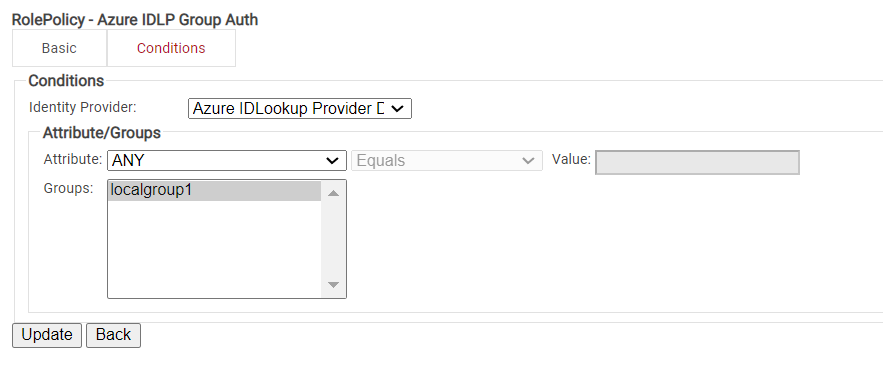
Cloud RADIUS can perform a User Group Lookup so we can create network access policies based on the Groups a user is in.
Configuring Policies
Cloud RADIUS can segment users and restrict/allow resources based on information stored in their directory entry.
The following policies need to be configured:
- Account Lookup Policy
- User Enrollment Role Policy
- Network Authentication Policies
- Default Fallback Role Policy
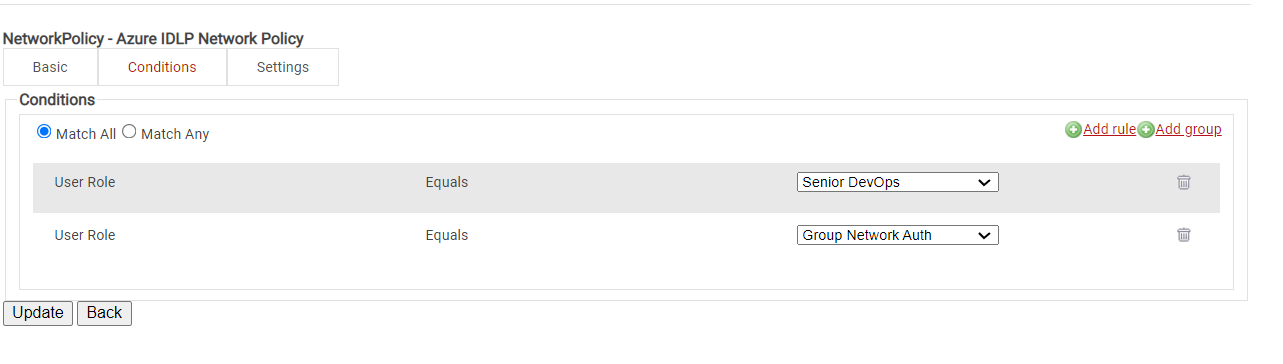
- Network Policy
To see the step-by-step process for each Policy, go to the Configuring Policies section on Configuring a Cloud RADIUS with Azure AD/Entra ID to Support WPA2-Enterprise.
Network Policies
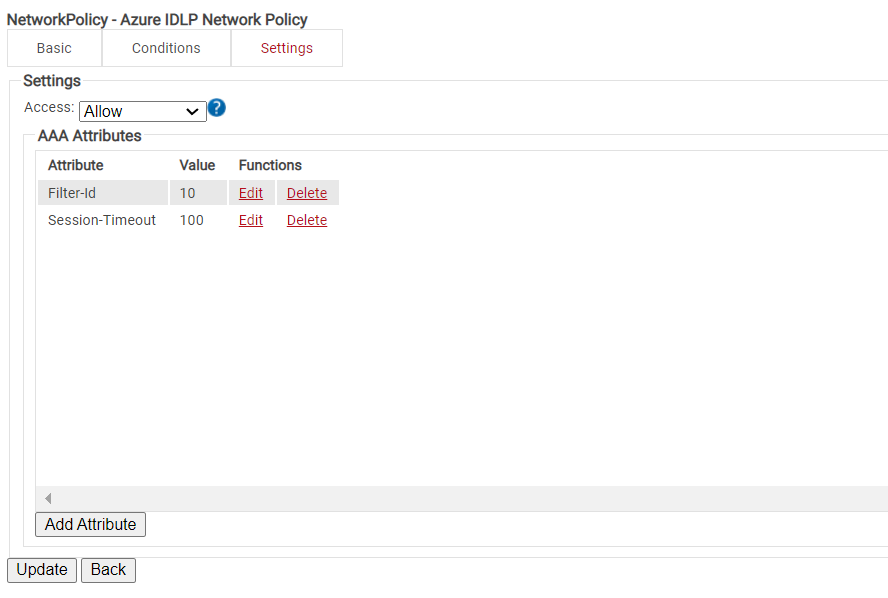
The purpose of a Network Policy is to specify how Cloud RADIUS will authorize access to a particular User Role. A typical Network Policy would say something like: “If User Role = Staff, authorize access and assign them to VLAN 2”. You can configure any RADIUS Attribute to be sent to the wireless controller. If you leave the attribute section blank, it will just send Access-Accept.
When to Use RADIUS Authentication for Microsoft Entra ID
RADIUS authentication is often a good choice for organizations that want to move identity management into the cloud while still maintaining control over network access.
You may want to consider this approach if you are trying to:
- Reduce reliance on passwords and move toward passwordless authentication
- Enable device-based authentication for managed endpoints
- Assign network permissions dynamically based on identity attributes
- Centralize authentication policies across wireless and remote access systems
- Implement multifactor authentication for VPNs, Wi-Fi access, RDGs, and other platforms that rely on RADIUS to authenticate users
If your environment still depends heavily on legacy directory infrastructure, a hybrid deployment may help simplify migration.
Security Best Practices for Azure RADIUS Authentication
Security is one of the primary motivations behind implementing RADIUS authentication with Azure AD or Microsoft Entra ID. When properly configured, certificate-based authentication helps reduce the risks associated with password-based network access while improving overall identity control within Microsoft Entra ID environments. Here are some of the best practices for security while integrating Azure AD/Entra ID with RADIUS.
Manage Certificate Lifecycle Carefully
Certificate lifecycle management is very important in passwordless authentication deployments. If a certificate is compromised, lost, or associated with a device that is no longer trusted, organizations should enable revocation mechanisms such as Online Certificate Status Protocol (OCSP) or Certification Revocation List (CRL) validation to prevent further network access.
Organizations should also monitor certificate expiration dates. Expired certificates can unintentionally block legitimate users from accessing network resources, which can create operational disruptions.
Prioritize Certificate-Based Authentication Methods
Whenever possible, organizations should use certificate-based authentication methods such as EAP-TLS instead of password-based protocols. Password authentication can introduce security risks, including credential replay attacks and phishing attempts. Certificate authentication reduces the need to transmit or store sensitive credentials during network login.
Automate Enrollment and Renewal Processes
Using MDM platforms like Microsoft Intune can help automate certificate issuance, renewal, and configuration deployment. Automation is especially valuable in large organizations where manually managing certificates would be impractical, and it helps ensure that endpoints remain compliant with organizational security policies throughout their lifecycle.
Enable Centralized Monitoring and Logging
Authentication events should be forwarded to centralized security monitoring systems whenever possible to improve threat visibility. Security teams can analyze authentication patterns to detect unusual behavior, potential compromise attempts, or unauthorized access trends.
Implement Network Segmentation Policies
Network segmentation is an important defense strategy in RADIUS authentication deployments. By assigning users or devices to specific network roles during authentication, organizations can limit access to sensitive systems, reducing the potential impact if a device or credential is compromised.
Review Identity and Access Policies Regularly
Identity policies within Microsoft Entra ID should be reviewed periodically as organizational structures and security requirements change. User roles, department assignments, and device compliance rules may need adjustment over time to reflect operational or security updates.
Frequently Asked Questions About Azure RADIUS Authentication
Does Azure AD support RADIUS natively?
No. Azure AD (Microsoft Entra ID) does not include a built-in RADIUS server. Organizations typically use external authentication services when implementing RADIUS authentication.
How does NPS compare with modern cloud RADIUS solutions?
Traditional Network Policy Server deployments require Windows Server infrastructure and may depend on directory synchronization. Many organizations prefer cloud-based RADIUS authentication solutions because they are easier to maintain and support passwordless workflows.
Can RADIUS authentication with Azure AD support MFA?
Yes. Multi-factor authentication can be enforced during certificate enrollment or through conditional policies configured inside Azure AD or Microsoft Entra ID.
Passwordless RADIUS with Azure AD/Entra ID
Setting up a secure, RADIUS-backed network can be daunting, but with SecureW2, it’s remarkably straightforward. You can have your network up and running in hours, fortified with industry-leading security measures. Our dedicated support team is always on hand to assist with any questions or issues that may arise, ensuring that your setup process is smooth and stress-free. We pride ourselves on our seamless integration with all SAML identity providers, which means you can avoid the usual headaches and complications of connecting different systems while enjoying our suite of Cloud RADIUS features.
At SecureW2, we understand that every organization has unique needs and budget constraints. That’s why we offer a range of affordable solutions tailored to fit organizations of all sizes. Whether you’re a small business or a large enterprise, we have a pricing plan that can work for you.
We have affordable solutions for organizations of all sizes; check out our pricing here or schedule a demo to see if we can help. Let SecureW2 be your partner in achieving a secure, efficient, and hassle-free networking environment.