How RADIUS Improves Wi-Fi Security | Wi-Fi RADIUS Authentication
As WiFi networks continue to expand, they have become a popular target for hackers. Cybercriminals have designed countless types of attacks, including man-in-the-middle attacks, to target users on wireless networks. But with the right defensive measures and technology, like a RADIUS server for WiFi, organizations can protect their networks from attack.
A Remote Authentication Dial-In User Service (RADIUS) server for Wi-Fi protects your networks by ensuring only authorized users can access them. RADIUS servers are seeing an increase in use across all types of businesses due to the wide array of security benefits they offer. In this article, we’ll examine what a RADIUS server can do for a Wi-Fi network, how Wi-Fi RADIUS authentication works, and why organizations should consider deploying this technology.
What is a RADIUS Server?
A RADIUS server is an authentication server that prevents unauthorized access to wired and wireless networks as well as VPNs. RADIUS servers are sometimes called AAA servers because they have authentication, authorization, and accounting capabilities:
- Authentication: When users or devices initially request access to the network, RADIUS servers authenticate them
- Authorization: RADIUS servers can also reference a directory of user information to determine the level of authorization individuals should be granted once they’ve been verified
- Accounting: RADIUS servers create RADIUS event logs that provide a detailed snapshot of the devices accessing a networking resource
There are many authentication protocols you can use alongside RADIUS. These protocols typically determine how an end user or device authenticates itself. The most popular options include credential-based authentication (username and password) and certificate-based authentication.
The Key Components of RADIUS Wi-Fi Authentication

To work successfully, RADIUS Wi-Fi authentication requires a few components beyond the standard password-based Wi-Fi authentication you see in home networks. It requires an enterprise-grade wireless access point, the RADIUS server itself, and a shared secret that keeps interactions between the client and server safe.
You’ll also need to determine what kind of authentication protocol you want to use in tandem with your RADIUS. The authentication protocol dictates which method users and devices will use to prove their identities when they request access.
RADIUS Wi-Fi Authentication Protocols

Before we get into how RADIUS Wi-Fi authentication works, it’s important to understand some of the more popular authentication protocols in use. Organizations typically use one of three protocols:
- EAP-TLS
- PEAP-MSCHAPv2
- EAP-TTLS/PAP
Here are the pros and cons of each of these protocols.
Extensible Authentication Protocol-Transport Layer Security (EAP-TLS)
EAP-TLS is a passwordless authentication protocol. Instead of logging into a wireless network with a username and password, the system issues digital certificates to users and devices for authentication. A digital certificate is like a virtual photo ID; it’s made of a template that contains a lot more information about the individual using it. One major advantage of digital certificates is that they can’t be stolen or transferred, which gives administrators a much higher degree of certainty about who’s actually on their network.
Certificate-based authentication requires a Public Key Infrastructure (PKI) to maintain and manage those certificates, which can be a significant barrier to entry. But with the right tools, such as onboarding technology, modern PKIs are now much easier to implement than they were in the past.
PEAP-MSCHAPv2 (Protected Extensible Authentication Protocol-Microsoft Challenge Handshake Authentication Protocol version 2)
PEAP-MSCHAPv2 is a common credential-based authentication protocol. It offers some improvements over previous iterations, such as using an encrypted EAP tunnel when passwords are transmitted over-the-air.
The biggest flaw of PEAP-MSCHAPv2 is its dependence on passwords. Even with some improvements over its predecessors, it’s still a vulnerable authentication protocol based on a hashing algorithm that has been compromised for decades. Even Microsoft has recommended that organizations consider certificate-based alternatives to PEAP-MSCHAPv2, such as EAP-TLS.
EAP-TTLS/PAP
This protocol is similar to PEAP-MSCHAPv2 in that it also uses credentials for authentication. Using credentials means it carries the same disadvantages that we mentioned in the previous section.
EAP-TTLS/PAP requires devices to verify a server certificate before connecting to a network, to ensure they don’t connect to the wrong one. After verification, the device sends the user’s credentials through an encrypted EAP tunnel, much like with PEAP-MSCHAPv2.
Unfortunately, it’s easy to misconfigure devices for EAP-TTLS/PAP, and a single mistake can lead to end users sending their usernames and passwords over-the-air in a cleartext format, which is easy for a hacker to intercept.
How Does RADIUS Wi-Fi Authentication Work?
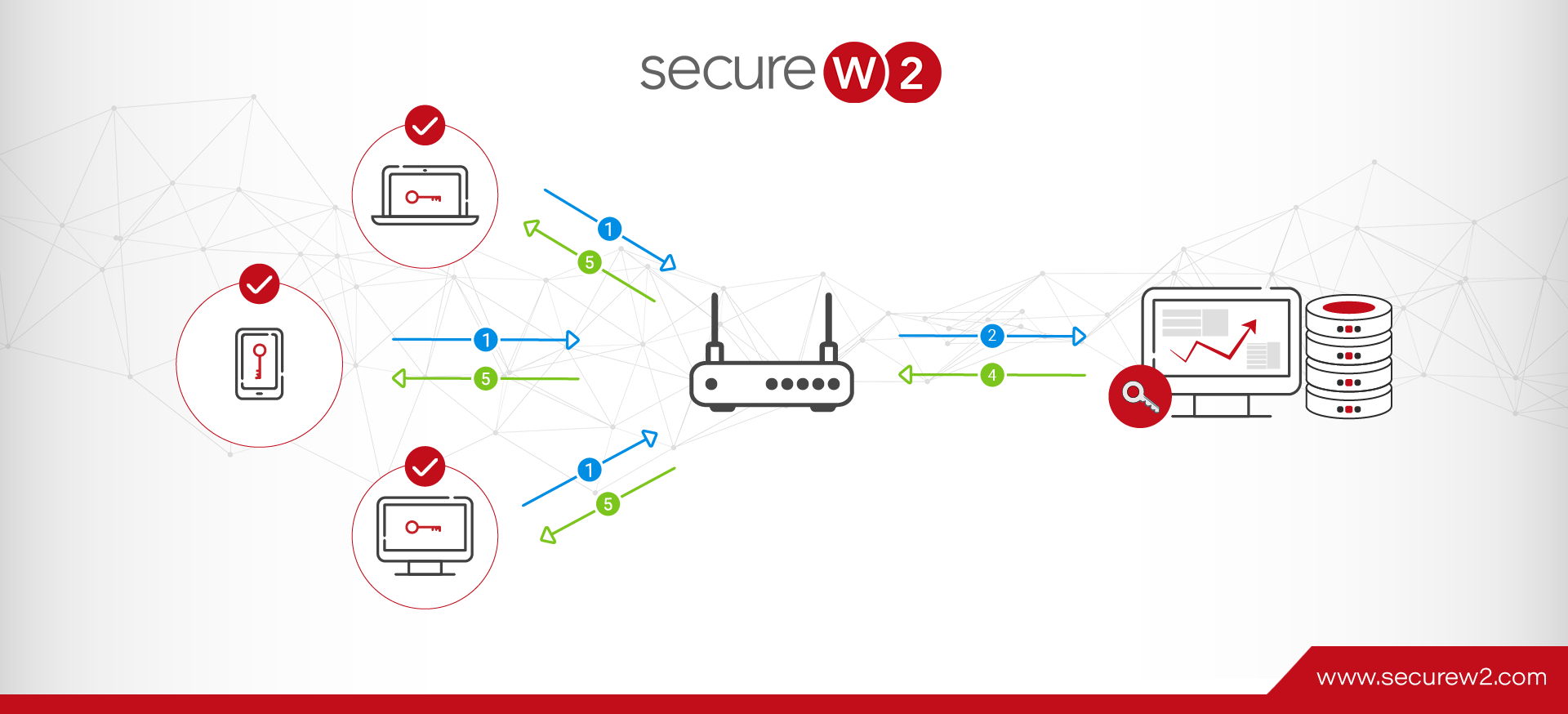
How RADIUS works with Wi-Fi security varies depending on the authentication protocol your network uses. For credential-based authentication protocols, those credentials are sent to the RADIUS server (generally through a protected tunnel), and then the RADIUS verifies them in the directory before granting access. The directory is usually an Identity Provider, such as Azure AD (Entra ID), Active Directory, Google, or Okta.
With EAP-TLS, which uses certificates for authentication, the process is a little different. The device starts by verifying the authenticity of the RADIUS server’s certificate . That way, the user is prevented from authenticating and connecting to the wrong network, which commonly happens in Evil Twin AP attacks. Next, the device sends its certificate to the RADIUS server, and the RADIUS checks whether the certificate is expired.
With the SecureW2 Cloud RADIUS platform, there’s an extra step. Cloud RADIUS integrates with all major cloud identity providers. At the time of authentication, it can communicate directly with Azure AD, Okta, Google, or OneLogin to verify the existence of a user once their certificate’s validity is confirmed. This ensures that the most up-to-date access policies are applied; even if you haven’t revoked the certificate yet, the user will be denied access if they’re deactivated in your IDP. Credentials aren’t sent over-the-air at all during this process, protecting them from exposure.
Common Use Cases for RADIUS Wi-Fi Authentication
Organizations in virtually every industry need to authenticate users and devices, determine authorization levels for each logged-in user, and track devices from a central location. RADIUS Wi-Fi authentication delivers all these capabilities. That’s why it’s in use across a wide range of environments.
RADIUS Wi-Fi for Enterprise and Corporate Networks
Organizations often use RADIUS Wi-Fi security to support their bring your own device (BYOD) programs. Rather than issuing pre-shared keys (PSKs) that leave their networks vulnerable to attacks and mismanagement, companies deploy a RADIUS server for Wi-Fi to let employees connect their personal devices by using their directory credentials.
Once users are on the network, companies can use VLAN segmentation capabilities within RADIUS to keep employees and contractors on separate network segments.
RADIUS Wi-Fi for Healthcare Organizations
The Health Insurance Portability and Accountability Act (HIPAA) has serious implications for Wi-Fi security at healthcare organizations. Many organizations rely on WPA2-Enterprise with 802.1X authentication to help them protect patient data from unauthorized access.
RADIUS accounting logs give them a detailed audit trail of which devices accessed which network resources — essential supporting information for passing a HIPAA audit.
RADIUS Wi-Fi for Higher Education
It’s challenging for higher education institutions to manage rapid device and user turnover at a large scale. Many organizations use RADIUS to help them authenticate thousands of users at once.
The eduroam service — which lets traveling students, faculty, researchers, and staff access the internet securely at participating campuses in 100 countries — uses 802.1X authentication and a linked hierarchy of RADIUS servers to verify users through credentials provided by their home institutions.
RADIUS Wi-Fi for Multi-Site Enterprises
Companies with multiple facilities can use RADIUS to manage authentication policies centrally. Working from a single RADIUS infrastructure, rather than on separate configurations in each office, IT teams can perform tasks like revoking a departing employee’s network access or authenticating guest users on the network.
How to Set Up a RADIUS Server for Wi-Fi
To set up RADIUS for Wi-Fi in your organization, you’ll first need to gain access to a RADIUS server, your wireless access points, your identity directory, and your authentication protocol and certificates. Although details may vary from platform to platform, you’ll probably follow these steps:
- Select and install RADIUS server software. You can implement on-premises or use a cloud-based RADIUS service.
- Register each wireless access point as a RADIUS client. Your access points will then be able to act as intermediaries between end-user devices and your RADIUS server.
- Select an EAP method. Choose between EAP-TLS, PEAP-MSCHAPv2, and EAP-TTLS/PAP.
- Define your network access policies. Configure policies that give authenticated user groups appropriate levels of network access.
- Configure each access point for WPA2/WPA3-Enterprise. You’ll also need to direct each access point to your RADIUS server’s IP address.
- Enable RADIUS accounting and test your connections. RADIUS accounting will log all your session data, giving you valuable insights for troubleshooting and compliance reporting.
How to Avoid RADIUS Wi-Fi Implementation Challenges
Although RADIUS technology has proven its reliability over the years, some IT teams do run into problems during implementation. Use these strategies to maximize your chances of a successful go-live:
- Configure all certificates carefully. Authentication often fails because a client device doesn’t trust the certificate authority (CA) that issued the RADIUS server’s certificate. Be sure to distribute this root CA certificate to all client devices before you attempt certificate-based authentication. Also, make sure you renew all your RADIUS server certificates before they expire — otherwise, you’ll experience sudden authentication failures across your network.
- Set up more than one RADIUS server for Wi-Fi. If your single RADIUS server goes down, all wireless users will lose network access. Consider establishing RADIUS redundancy, in which another RADIUS server takes over when the primary server fails or is overloaded. Having more than one RADIUS server for Wi-Fi helps you avoid the security risks that come with downtime.
- Make sure your firewalls aren’t blocking RADIUS traffic. RADIUS authentication and RADIUS accounting use UDP ports 1812 and 1813, respectively. These ports must be open on any firewall sitting between your access points and your RADIUS server. Otherwise, a firewall that separates your subnets will simply drop RADIUS packets.
- Verify that Network Time Protocol (NTP) is working correctly on your RADIUS servers and on all client devices. NTP helps synchronize the clocks on all devices on your network. If a device’s clock is off by more than a few minutes, it may determine that the current time doesn’t fall within the validity period of the RADIUS server’s certificate. This discrepancy will prevent authentication.
- Check for shared secret consistency. If the shared secret isn’t identical on the RADIUS server and on the access point, all authentication attempts through that access point will fail. One way to ensure consistency while also reducing security risk is to generate shared secrets randomly and store them in a secrets manager.
The Security Risks of Credential-Based Wi-Fi Authentication
While using credentials for Wi-Fi authentication is typically one of the simplest routes to take, it’s far from the most secure. Organizations tying their Wi-Fi to passwords expose their networks to many risks, including:
- Vulnerability to Over-the-Air Attacks
- Password Mismanagement
- Poor End-User Experience
- Increased IT Workload
Vulnerability to Over-the-Air Attacks
Transmitting sensitive information over the air is always a risk, even with rigorous security practices in place. Tying your network access to these credentials and requiring users to send them over-the-air is a tremendous risk.
There are many attack vectors designed to intercept communications transmitted wirelessly. From the variety of man-in-the-middle attacks to Evil Twin AP attacks that trick end users into sending their credentials to the wrong place, there are plenty of ways to target credentials through password-based authentication methods.
The best way to keep your credentials secure is to limit their use as much as possible. This means choosing a way to authenticate users that doesn’t involve exposing their credentials to unnecessary risk.
Password Mismanagement
One of the most challenging aspects of passwords is managing them. The average user maintains many passwords nowadays, and remembering them all is a hassle. Because of this, it’s common to repeat passwords or only vary them slightly between accounts. Some users may even default to using extremely insecure, simple passwords that can easily be guessed in attacks such as dictionary attacks.
Another issue in mismanagement is the sharing of passwords. If you’re using a pre-shared key (PSK) network based on a single password, and that password has been shared with more than several people, you can safely assume they’ve shared it with others.
Poor End-User Experience
Aside from the security issues that come with managing multiple passwords, there’s the end-user experience to consider. Juggling dozens of passwords is frustrating. It becomes exponentially harder when organizations implement strict access control policies based on passwords, such as having to change passwords regularly and imposing specific complexity requirements.
Passwords make user access difficult. And if a user ever forgets their password or doesn’t change it in time before expiration, things become more complicated.
Increased IT Workload
One primary difference we’ve heard from organizations that implemented certificate-based authentication is the unexpected drop in support tickets. End users are bound to forget passwords once in a while, and when this happens, they need to reach out to your support team to regain access to the network.
Besides being annoying for end users, who experience a drop in productivity while they wait, this is time-consuming for your IT department. Some surveys have shown that a single password reset can cost $2,700, which isn’t surprising when you factor in how long the ticket takes to resolve.
Benefits of Certificate-Based Authentication & RADIUS Servers for Wi-Fi
The alternative to password-based authentication is certificates. Using certificates for user authentication provides a range of benefits, especially when combined with the security of a RADIUS server:
- Improved Security Based on Cryptography
- Enhanced Ability to Enforce Granular Network Access Control Policies
- Easier End-User Login Experience
- Ability to Integrate with Your Existing Network Infrastructure
Improved Security Based on Cryptography
Implementing a RADIUS authentication server for your Wi-Fi access is already a step forward, but it’s enhanced when you bring in the cryptography offered by digital certificates. Certificates use robust asymmetric encryption to prevent the open transmission of sensitive data over the air. Each one is composed of a private key and a public key, which are mathematically linked to one another.
Because the system is no longer sending credentials to your wireless access points, many attacks are prevented. For example, man-in-the-middle attacks can’t steal passwords. Even if the attackers intercept a certificate, they cannot use or transfer it, since the private key is never sent over-the-air.
Enhanced Ability to Enforce Granular Network Access Control Policies

To manage and deploy certificates, you need a PKI. You can use the PKI along with a RADIUS server for Wi-Fi to leverage information from your infrastructure, including your directory services or mobile device management (MDM) platforms.
Certificate templates contain much more detailed information than anything you get from a username and password. Some of this information comes from your identity provider and MDM, and you can apply it to your network access policies. Our Cloud RADIUS service can segment users into different VLANs based on their user group. For example, you can segment your HR employees from your DevOps employees who may need more bandwidth.
Easier End-User Login Experience
Passwordless authentication offers a better experience for your end -users. At the same time, it enhances security. It saves users the time they would otherwise have to spend re-entering complex passwords. It also gives them one less password to worry about remembering because certificates allow them to connect automatically. The authentication process with certificates is also slightly faster.
Ability to Integrate with Your Existing Infrastructure
Both RADIUS and PKI can integrate with your network infrastructure, including with Identity Providers such as Microsoft Active Directory, Azure AD (Entra ID), Google, and Okta. Our Cloud RADIUS integrates seamlessly with your identity provider through the Identity Lookup process, which verifies a user’s status in real time during each authentication.
Why Choose Cloud-Based RADIUS?
For decades, organizations have used on-premises RADIUS servers to manage access, authorization, and accounting on their Wi-Fi networks. Despite the many benefits of on-premises RADIUS, it comes with potential drawbacks. Organizations must:
- Provide a dedicated operating system to patch
- Put a RADIUS server and identity infrastructure in every office that needs low-latency authentication
- Maintain RADIUS software
- Build and operate a high-availability architecture
- Hire an in-house team who can troubleshoot authentication failures on short notice
In recent years, organizations have begun achieving the benefits of RADIUS without the overhead by implementing cloud-based RADIUS solutions. With cloud RADIUS:
- A provider handles infrastructure provisioning, OS patching, high availability, and failover as a service
- The organization maintains control over authentication policies and connects access points
- Multi-site organizations can enforce policies consistently across locations
- Policy changes go out to all locations immediately
Cloud-based RADIUS does depend on internet connectivity to work, and it may not be an option for organizations that are legally required to handle all data on-premises. But for many organizations, especially those that already use cloud-based identity providers, it’s an appealing option.
SecureW2 Makes RADIUS Server & PKI Security for Wi-Fi Accessible & Simple
While RADIUS server configuration and setup isn’t usually intimidating for organizations, implementing a PKI can be. We often hear administrators say the more they’re involved with a PKI, the less they want to manage it.
Fortunately, with the right platform, deploying a PKI and RADIUS doesn’t need to be challenging. The SecureW2 JoinNow Platform is a passwordless authentication suite that provides organizations with everything they need to deploy passwordless security for their wireless networks.
Our suite includes Cloud RADIUS and Dynamic PKI. Both solutions were designed with vendor neutrality in mind, integrating with a wide range of vendors. With the SecureW2 JoinNow Platform, you can manage and automate the entire certificate lifecycle and create granular network policies — all from one location.
See for yourself how RADIUS and Wi-Fi security looks in action. Contact our expert solutions engineers today to schedule a demo.